Brief Description
GDPR is the General Data Protection Regulation that was agreed upon by the European Parliament and European Commission in late 2016 to be affected in May 2018. This GDPR will override all other data protection laws and provide a single unified regulation. The policy affects 28 European Union member countries.
VMware NSX allows virtualised network in a software-defined data centres It decouples the system from the hardware making the network elastic, allowing you to create, grow, delete, and shrink the network as needed.
This article covers how VMware NSX helps companies and organisations to achieve GDPR compliance.
Overview
The purpose of the GDPR is to increase the scope of existing regulation, i.e. make it standardised for all EU member countries. A notable change introduced by the GDPR is the penalties in the event of a personal data breach which can be hefty, and companies need to watch out. Companies and organisations need to make the necessary changes to prepare for the enactment of this significant change. It will involve looking closely at how they store, handle and exchange data in the face of the ever-evolving threat landscape. Some of the changes that the enforcement of the GDPR will bring include;
- Large organisations are required to employ a Data Protection Officer (DPO) who is in charge of dealing with any data issues such as cyber-attacks or any other kind of breach.
- Companies are required to file a Data Protection Impact Assessment (DPIA) to ensure complete compliance with the GDPR. The DPO is expected to give access to the audit once a year.
- The DPO is required to report a breach as soon as possible (72 hours) to the Supervisory Authority.
- The data protection measures will be reviewed to minimise breaches and ensure compliance with the GDPR.
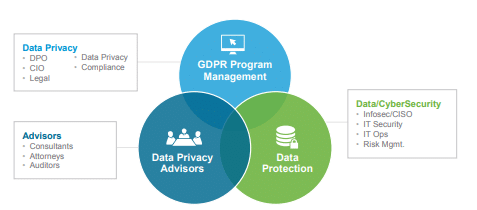
Fig 1. Three functional areas the GDPR is focusing on
These are the three main essential areas that the GDPR compliance will target.
Achieving GDPR compliance with VMware NSX
VMware NSX allows one to deploy security controls inside the data centre network at a much favourable cost compared to deploying a hardware equivalent. It is also straightforward to implement and operate. VMware NSX uses ISO framework to validate the VMware NSX products that can be applied to match GDPR requirements. The features that make this software favourable for GDPR compliance include:
NSX provides a zero-trust security model
In a zero-trust security model, the network is virtualised, and all resources are accessed securely regardless of location and control is on a need to know.
One can inspect and log all traffic from any source or destination as it allows for micro-segmentation of the network. Micro-segmentation separates the security visibility and control domain into two parts: the end node and the security control. The security controls must be distributed and have enough performance. NSX also automates the repair of any compromised VM.
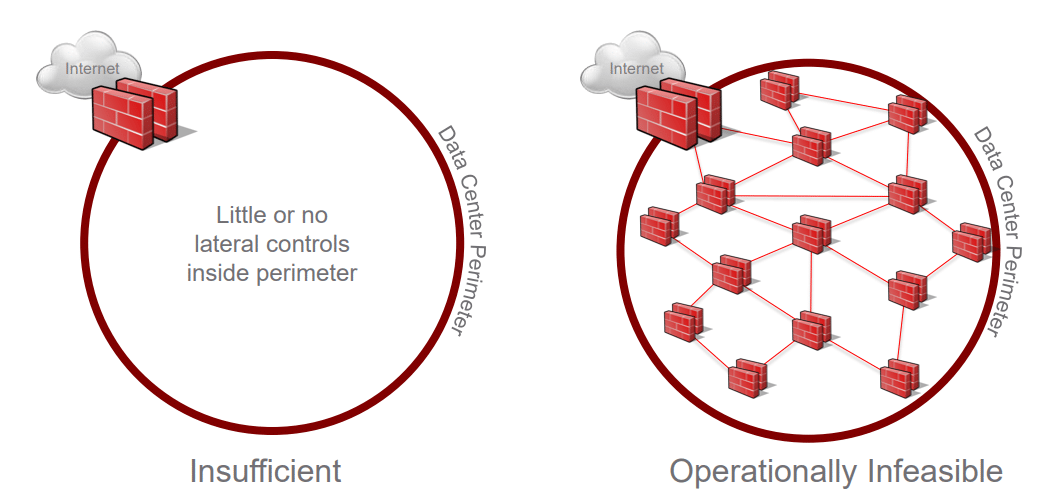
Fig 2. Perimeter-centric vs micro-segmentation network security
As seen in Figure 2 above, micro-segmentation makes it easy to monitor data and is operationally feasible, unlike perimeter-centric network security. This is because there are very few lateral controls inside the perimeter.
Intelligent grouping
VMware NSX has a smart grouping capability of NSX Service Composer with the distributed firewall. Perimeter security and zoning are insufficient and cumbersome.
The Service Composer allows one to create groups coined “Security groups”. They can have dynamic membership criteria which can be part of the computer name of a Virtual Machine, its guest Operating System name or the VM name.
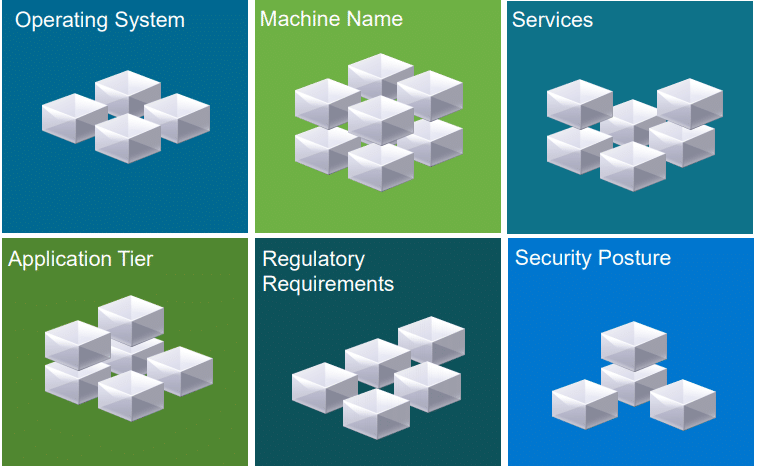
Fig 3. Groups defined by customised criteria
These are some of the security groupings that are created to ease management of the network.
Data Privacy Impact Assessment (DPIA)
NSX will help organisations and their Data Protection Officer to build their DPIA by delivering a real-time security overview that is realistic on the whole Datacenter. It is inclusive of:
- Real-Time visibility into the security group memberships & effective firewall rules for a VM, between VMs and between VM and the physical network.
- Datacenter time machine – it tracks changes in the system for troubleshooting or audit purposes.
- Compliance Engine which has a Simple Search Interface used to write policies and set alerts.
- Instantly raises the alarm upon policy violation and non-compliance.
Minimizing risk
Security groups allow building flexible and highly adaptive, applications centred security policy where VMs are stored after they are allocated, and inherit their firewall rules per the application’s requirements.
Real-time security level monitoring
By driving policy-based solutions more rooted into the network, NSX eliminates the need for complicated and time-consuming network configuration. This can help an organisation to check the system for attacks in real-time, handle any threats and provide the latest and most appropriate advice on safeguarding your data.
Allows you to move workloads seamlessly
NSX runs VMs and all their connected networks security policies between data centres in very few minutes. It avoids interrupting the running application, enabling active-active data centres and immediate distracted recovery options.
Conclusion
The implementation of the GDPR will have a significant impact on the businesses operating within the EU or dealing with European personal data. VMWare NSX is one of the tools that can be used to control where workloads can send and receive data effectively. It uses a micro-segmentation architecture which allows for real-time monitoring of data movement across the network. It increases an organisation’s competitiveness and helps in the timely resolution of a data breach and in conducting a Data Compliance Audit.
Xieles Support can help you with the installation of any Cloud Computing or Cloud Hosting environments and related tools. Get a quote from us if you need any assistance.
STILL SPENDING TIME ON SUPPORT?
Outsource your helpdesk support to save time and money. We have technicians available for little over 5 USD per hour in order to assist your customers with their technical questions. Grow your business and concentrate more on your SALES!
Xieles Support is a provider of reliable and affordable internet services, consisting of Outsourced 24×7 Technical Support, Remote Server Administration, Server Security, Linux Server Management, Windows Server Management and Helpdesk Management to Web Hosting companies, Data centers and ISPs around the world. We are experts in Linux and Windows Server Administration, Advanced Server Security, Server Security Hardening. Our primary focus is on absolute client satisfaction through sustainable pricing, proactively managed services, investment in hosting infrastructure and renowned customer support.